FortiOS 8.0 and What It Means for Enterprise Security

Fortinet released FortiOS 8.0 on 10 March 2026 at its annual Accelerate conference — the most significant update to its Security Fabric platform in years. For Philippine enterprises running FortiGate firewalls, this release has practical implications that go well beyond a routine patch cycle.
Here is what changed, why it matters, and what you should do next.
Shadow AI Is Now a Documented Network Risk
Fortinet's own data puts the share of unsanctioned generative AI applications on enterprise networks at 98%. Employees are accessing tools — ChatGPT, Gemini, open-weight models, AI coding assistants — without IT visibility, data governance controls, or any policy enforcement.
FortiOS 8.0 introduces FortiView for AI, a real-time dashboard that maps every AI application touching your network. It distinguishes approved tools from shadow AI, flags risky usage patterns, and enforces policy at the application layer. For Philippine organizations in BFSI, BPO, healthcare, or government — sectors where data confidentiality is non-negotiable — this is not a nice-to-have. Unmanaged AI usage is an active data leakage vector, and local regulators are beginning to take notice.
If your FortiGate hardware is running firmware below 8.0, you have zero native visibility into this exposure today.
Post-Quantum Cryptography Moves into Production
Quantum computing threats to classical encryption are no longer theoretical. FortiOS 8.0 ships post-quantum cryptography (PQC) across the Security Fabric by default, using ML-DSA certificates for authentication and key establishment on agentless VPN connections and management interfaces.
This matters because of a well-documented attack strategy called "harvest now, decrypt later" — adversaries capture encrypted traffic today and decrypt it once quantum hardware matures. For Philippine enterprises holding long-retention data — financial records, healthcare files, government contracts — waiting for quantum computing to go mainstream before acting is the wrong posture.
FortiOS 8.0 makes the PQC migration less disruptive than any prior release. The practical first step is updating VPN and remote access endpoints to PQC-capable configurations.
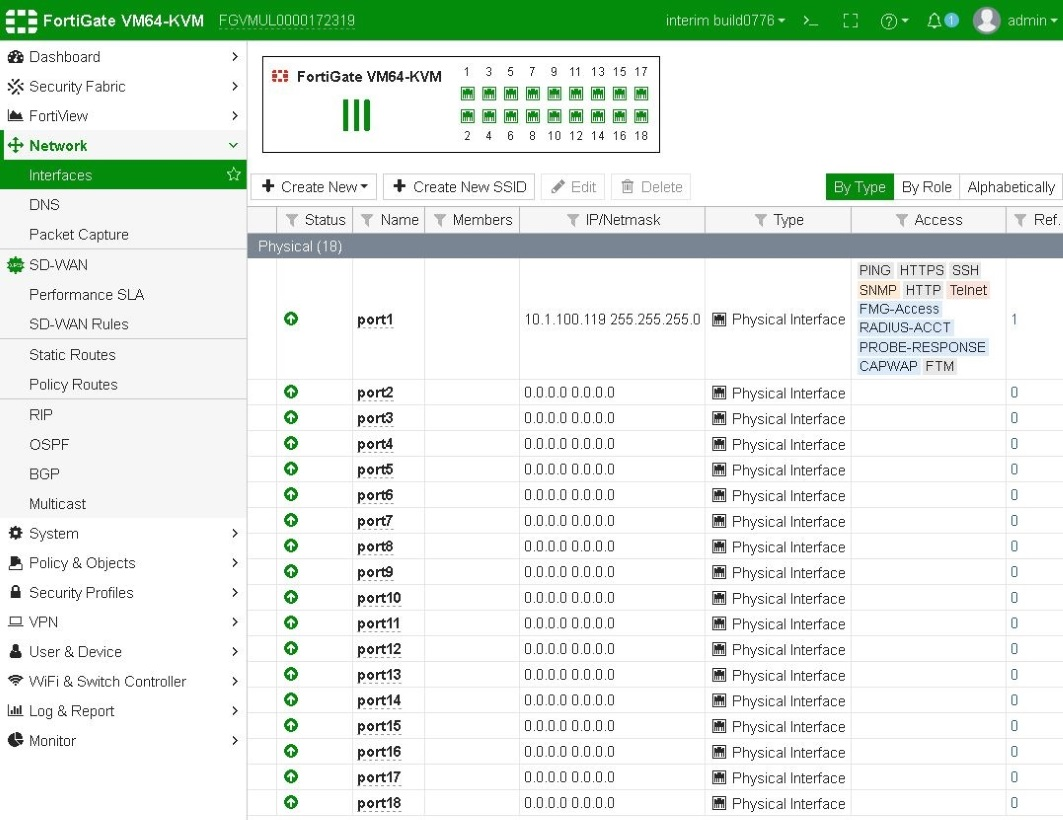
SD-WAN Gets Simpler Without Losing Visibility
FortiOS 8.0 consolidates SD-WAN configuration into unified bundles and introduces multipath IPsec tunnels. This directly addresses the operational complexity that has made SD-WAN expensive to manage for organizations with provincial branches — Cebu, Davao, Clark, Iloilo — where WAN reliability is uneven and multi-link failover is business-critical.
The new AI Fabric Agents add conversational troubleshooting to firewall and SD-WAN environments. Engineers can query the system in natural language to diagnose performance issues rather than parsing logs manually. For lean IT teams — which describes most Philippine SMEs and mid-market companies — this shortens time-to-resolution on connectivity incidents without requiring additional headcount.
Sovereign SASE for Local Data Residency
The Philippines' data center sector is expanding fast. Capacity is projected to triple to 473 MW by 2028, and the Data Center Operators of the Philippines is actively advancing data localization policy frameworks.
FortiOS 8.0's SASE Outpost feature allows organizations to deploy sovereign SASE — keeping traffic inspection, logging, and policy enforcement within a defined geographic boundary. For Philippine companies evaluating hybrid work infrastructure, this means full SASE architecture — secure web gateway, CASB, zero trust network access — without routing sensitive data through overseas points of presence. As local data residency requirements tighten, that is a material compliance advantage.
Four Actions Worth Taking Before Q3 2026
1. Audit your current FortiOS version. Any deployment below 8.0 lacks shadow AI visibility and PQC support. A firmware status check takes an afternoon.
2. Map your AI application exposure. Run a short internal survey before enabling FortiView for AI. Knowing which teams are using which tools makes the policy configuration faster and more accurate.
3. Review your VPN endpoints. Identify remote access and site-to-site tunnels that need PQC certificate migration. Planned, this is low-disruption. Forced, it is not.
4. Evaluate SASE Outpost if you have branch offices. Organizations with regional footprints stand to benefit most from sovereign SASE — both for performance and for compliance positioning.
One hardware note before you plan: the FortiGate 100F reached end-of-sale in April 2026 and will not support FortiOS 8.0. If your appliances are due for refresh, aligning that cycle with this release is the right call — you get the new security capabilities without a second migration in 18 months.
Talk to our I.T. Hardware team →